iran drone swarm tactics analysis is the core query behind this page, and the practical conclusion is that swarm effectiveness comes from sequencing and adaptation rather than raw platform count. Timing dispersion, decoy layering, and reconnaissance feedback loops are what turn low-cost systems into high-pressure campaign tools.
This briefing treats swarm activity as an evolving tactic set that forces defenders to spend decision bandwidth as well as interceptors. The model below tracks how warning windows, command friction, and posture shifts interact over repeated strike cycles.
Pair Iran Drone Swarm Tactics Analysis with Gulf Air Defense Interceptor Capacity, Iran Missile Attack Risk Index, and Proxy Escalation Ladder Middle East when the goal is to connect saturation timing and decoy effectiveness to adjacent timeline, capability, and escalation questions without forcing readers back through the full archive.
How Swarm Sequencing Compresses Warning Time
Swarm sequencing matters because defenders are not solving one problem; they are solving timing, classification, and allocation at the same time. Launches that are staggered just enough to stretch decision-making can be more effective than a single mass wave because they keep operators from resetting cleanly between engagements. Warning time is compressed not only by speed, but by uncertainty over which track matters most.
That is why this page should be read alongside Gulf Air Defense Interceptor Capacity. A swarm does not need to break every layer to be useful; it only needs to force the defender into inefficient timing and poorer allocation.
| Variable | Current Signal | Risk Implication | Tracking Rule |
|---|---|---|---|
| Launch dispersion | Rising | Higher near-term uncertainty | Confirm over two windows |
| Track prioritization | Mixed | Potentially bounded escalation | Reassess after policy updates |
| Interceptor allocation | Stable | De-escalation path possible | Track persistence vs narrative shift |
Decoys, Reconnaissance Loops, and Defensive Fatigue
Decoys are strategically valuable because they attack confidence as much as hardware. If defenders cannot quickly separate mission-relevant drones from low-cost distractors, they spend attention, ammunition, and time on the wrong tracks. Over repeated nights that fatigue becomes a campaign effect in its own right.
Reconnaissance loops make the tactic more dangerous because they turn each defensive response into data for the next wave. A swarm is not just a launch event; it is a learning cycle. That is one reason drone pressure often fits naturally into the broader Proxy Escalation Ladder Middle East rather than remaining a purely tactical story.
What Makes a Swarm Operationally Effective
An effective swarm is not defined by the number of airframes launched; it is defined by whether the different elements share a usable mission logic. Reconnaissance assets, decoys, one-way attack drones, and follow-on systems all need to create pressure at the same moment against the same defensive problem. If those layers are not synchronized, the swarm becomes expensive noise rather than a useful tactical instrument.
The best indicator of effectiveness is whether the swarm changes the defender's behavior. If air defenses shift posture, high-value activity pauses, or interceptors are burned at a pace that changes tomorrow's risk picture, then the swarm worked even if the visible physical damage was limited.
| Variable | Current Signal | Risk Implication | Tracking Rule |
|---|---|---|---|
| Recon quality | Rising | Higher near-term uncertainty | Confirm over two windows |
| Command coherence | Mixed | Potentially bounded escalation | Reassess after policy updates |
| Recovery tempo | Stable | De-escalation path possible | Track persistence vs narrative shift |
Interception Economics in Prolonged Exchange Cycles
Interception economics is one of the clearest reasons swarms matter. Attackers often accept attrition because low-cost systems can still impose high-cost defensive behavior. Defenders, by contrast, are forced to preserve expensive inventories, maintain constant readiness, and make rapid judgment calls under uncertainty. The imbalance is not only financial; it is organizational.
That is why prolonged swarm use should be treated as an endurance contest rather than a single exchange. If a defender spends faster than it regenerates, the tactical picture on night one can be very different from the campaign picture on night four. Readers should compare this section with Iran Missile Attack Risk Index when drone and missile pressures begin to overlap.
Command-and-Control Friction as a Strategic Target
Swarm tactics are dangerous partly because they turn command-and-control into a target even without a direct strike. High-volume alerts force operators to prioritize, reclassify, and communicate under compression. A defender that still destroys most inbound drones can nevertheless lose effectiveness if the command network becomes slower, noisier, or more error-prone.
That makes human performance and fallback procedures part of the military balance. Operations rooms need rotation plans, simplified engagement logic, and redundant communications if they want to absorb repeated drone pressure without compounding mistakes.
| Variable | Current Signal | Risk Implication | Tracking Rule |
|---|---|---|---|
| Comms resilience | Rising | Higher near-term uncertainty | Confirm over two windows |
| Operator rotation | Mixed | Potentially bounded escalation | Reassess after policy updates |
| Fallback protocols | Stable | De-escalation path possible | Track persistence vs narrative shift |
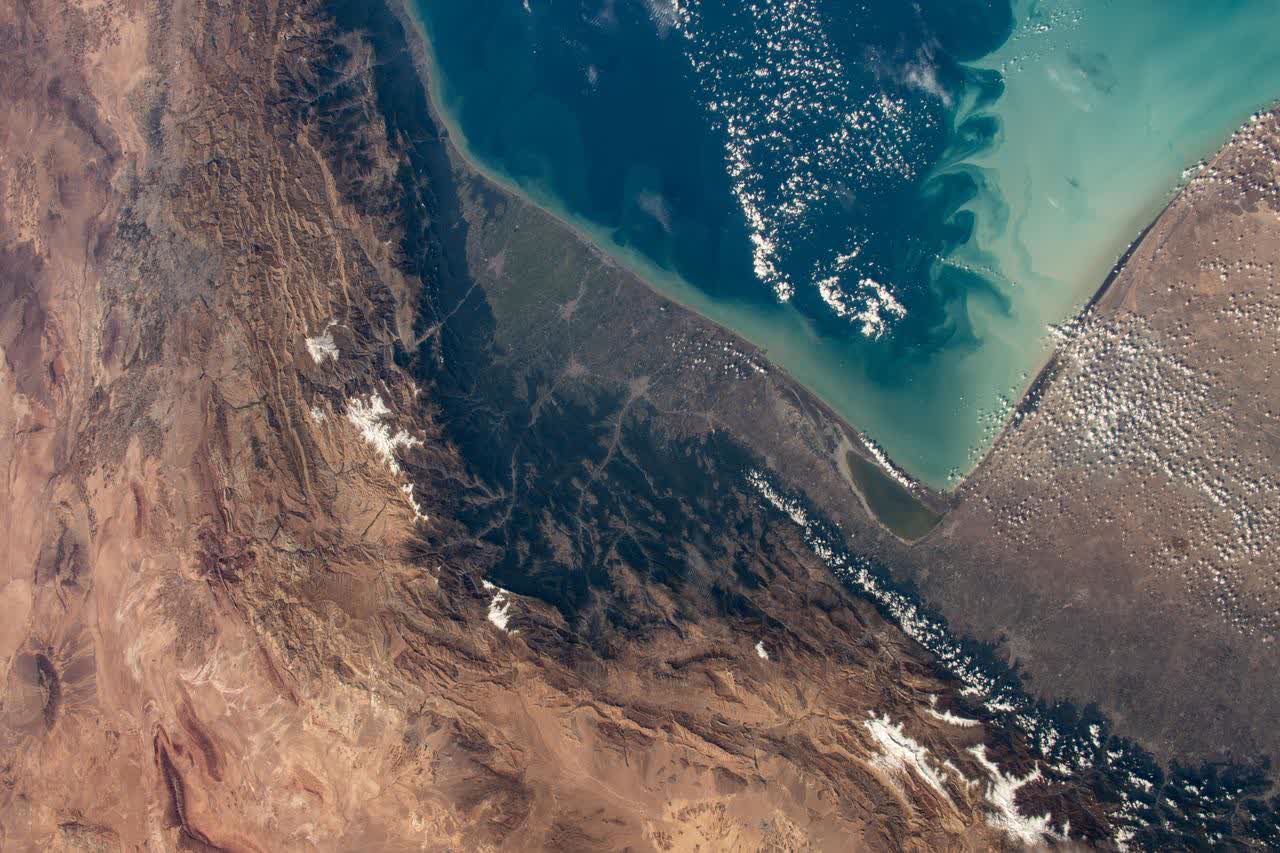
How Geography Shapes Swarm Corridor Design
Geography shapes swarm effectiveness because low-flying or slow systems gain value from clutter, masking, and route diversity. Littoral corridors, industrial background noise, and terrain edges can all complicate detection and tracking. Good swarm design uses geography to force defenders into awkward sensor problems before the first intercept decision is made.
That is why drone analysis belongs next to geography pages rather than apart from them. Readers trying to understand corridor design should compare this page with Persian Gulf Map and Gulf of Oman Map Airspace Closures Map Hormuz Strait Map, where route space and radar geometry shape how much warning defenders really get.
Indicators That Distinguish Signaling from Campaign Use
A signaling strike is usually narrow, dramatic, and easy to narrate. Campaign use looks different: recurrence increases, target sets widen, adaptation becomes visible, and the attacker starts probing for patterns rather than sending one message. That distinction matters because readers often overread a single wave and underread the operational learning that follows it.
The quickest way to tell the difference is to watch what changes between events. If routing, timing, target logic, and supporting messaging all evolve, the swarm is being used as an adaptive campaign tool. If everything stays theatrical and isolated, it is more likely a signaling action.
| Variable | Current Signal | Risk Implication | Tracking Rule |
|---|---|---|---|
| Recurrence pattern | Rising | Higher near-term uncertainty | Confirm over two windows |
| Target depth | Mixed | Potentially bounded escalation | Reassess after policy updates |
| Messaging alignment | Stable | De-escalation path possible | Track persistence vs narrative shift |
Defensive Mitigation Stack for High-Volume Events
Defensive mitigation works best as a stack rather than a single technology answer. Sensor fusion, low-cost engagement options, hard-kill and soft-kill layering, and rapid repair capacity all matter because a swarm is trying to overwhelm the system, not just one launcher. The strongest defensive design is the one that keeps critical output functioning even when perfect interception is impossible.
That means prioritization rules have to be explicit before the event, not invented during it. Defenders need to know which assets are protected first, which tracks are tolerated, and what level of damage is acceptable in order to preserve broader campaign resilience.
Market and Narrative Spillover from Swarm Activity
Swarm events often travel beyond the tactical sphere faster than their physical results would suggest. Because they are visible, numerous, and easy to narrate, they can move insurance pricing, market sentiment, and public fear quickly. That does not make the narrative false; it means the narrative can outrun the damage picture.
Analysts should therefore separate direct operational effect from wider spillover. If a swarm coincides with maritime anxiety or regional energy concerns, the market effect can be outsized relative to immediate military damage. That is why swarm reporting frequently overlaps with pages like Strait of Hormuz Shipping Freeze.
| Variable | Current Signal | Risk Implication | Tracking Rule |
|---|---|---|---|
| Media tempo | Rising | Higher near-term uncertainty | Confirm over two windows |
| Insurance reaction | Mixed | Potentially bounded escalation | Reassess after policy updates |
| Policy cadence | Stable | De-escalation path possible | Track persistence vs narrative shift |
72-Hour Monitoring Framework for Analysts
A strong 72-hour framework should track recurrence, route adaptation, target breadth, defensive posture changes, and the ratio between successful penetration and mere alert generation. Those signals should be scored over time rather than summarized once, because swarm tactics often reveal their true purpose only after the second or third cycle.
The main discipline rule is to revise the branch only when multiple variables move together. A noisier night, on its own, is not enough. But a noisier night plus different routing, more defensive strain, and a broader target set is a real change in the campaign picture.
How This Analysis Connects to Broader Iran War Coverage
Drone swarms should not be treated as a self-contained niche. They connect directly to missile warning problems, base-defense endurance, escalation law, and shipping risk. A swarm may be tactically modest and still strategically important if it changes how commanders allocate interceptors or how policymakers assess the next retaliation window.
That is why this page sits in the middle of a broader cluster. Readers should move from Iran Missile Attack Risk Index to Gulf Air Defense Interceptor Capacity and then to Are We At War With Iran Now? when the question becomes less about tactics and more about what the tactic is doing to the overall crisis.
| Variable | Current Signal | Risk Implication | Tracking Rule |
|---|---|---|---|
| Tactical layer | Rising | Higher near-term uncertainty | Confirm over two windows |
| Strategic layer | Mixed | Potentially bounded escalation | Reassess after policy updates |
| Economic layer | Stable | De-escalation path possible | Track persistence vs narrative shift |
Operational Bottom Line for Decision Teams
The operational bottom line is that swarm risk rises fastest when three things happen together: route diversity improves, defender decision time shrinks, and the attacker shows visible adaptation between waves. Those are the moments when drone activity stops being a nuisance and starts functioning as a real campaign stressor.
Decision teams should therefore watch for change rather than spectacle. If the swarm is learning, the defender is tiring, and adjacent strike domains are becoming more active, the alert band should move up even before a single headline event forces that conclusion.

FAQ: Iran Drone Swarm Tactics Analysis
What defines effective swarm tactics in this conflict model?
Effective swarm tactics combine timing dispersion, reconnaissance feedback, and adaptive routing so defenders must solve multiple problems simultaneously.
Why are decoys strategically important?
Decoys absorb attention and interceptor capacity, increasing the chance that mission-relevant assets reach high-value windows.
How can analysts tell if swarm activity is escalating?
Look for repeated multi-session use, broader target logic, and tighter integration with messaging and other strike domains.
What should readers track over the next 72 hours?
Track recurrence, defensive posture changes, and whether command continuity indicators degrade across repeated cycles.
External references: CSIS, IISS, Reuters Middle East.