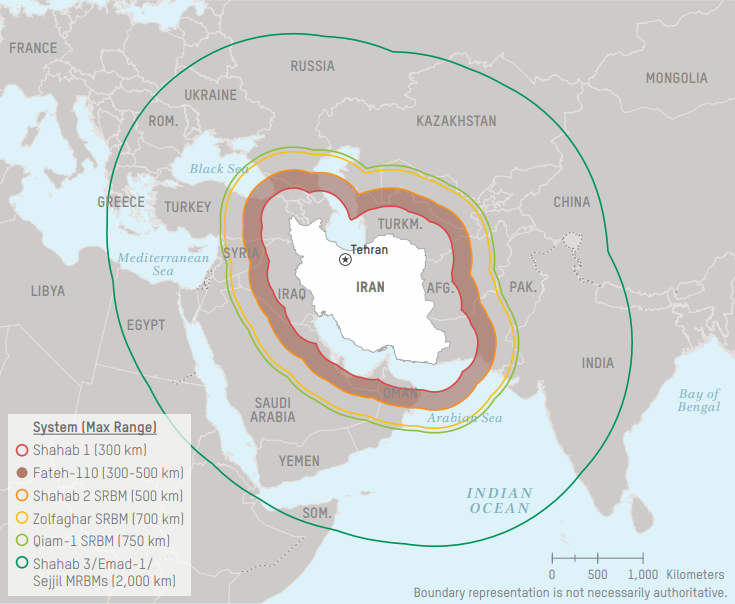
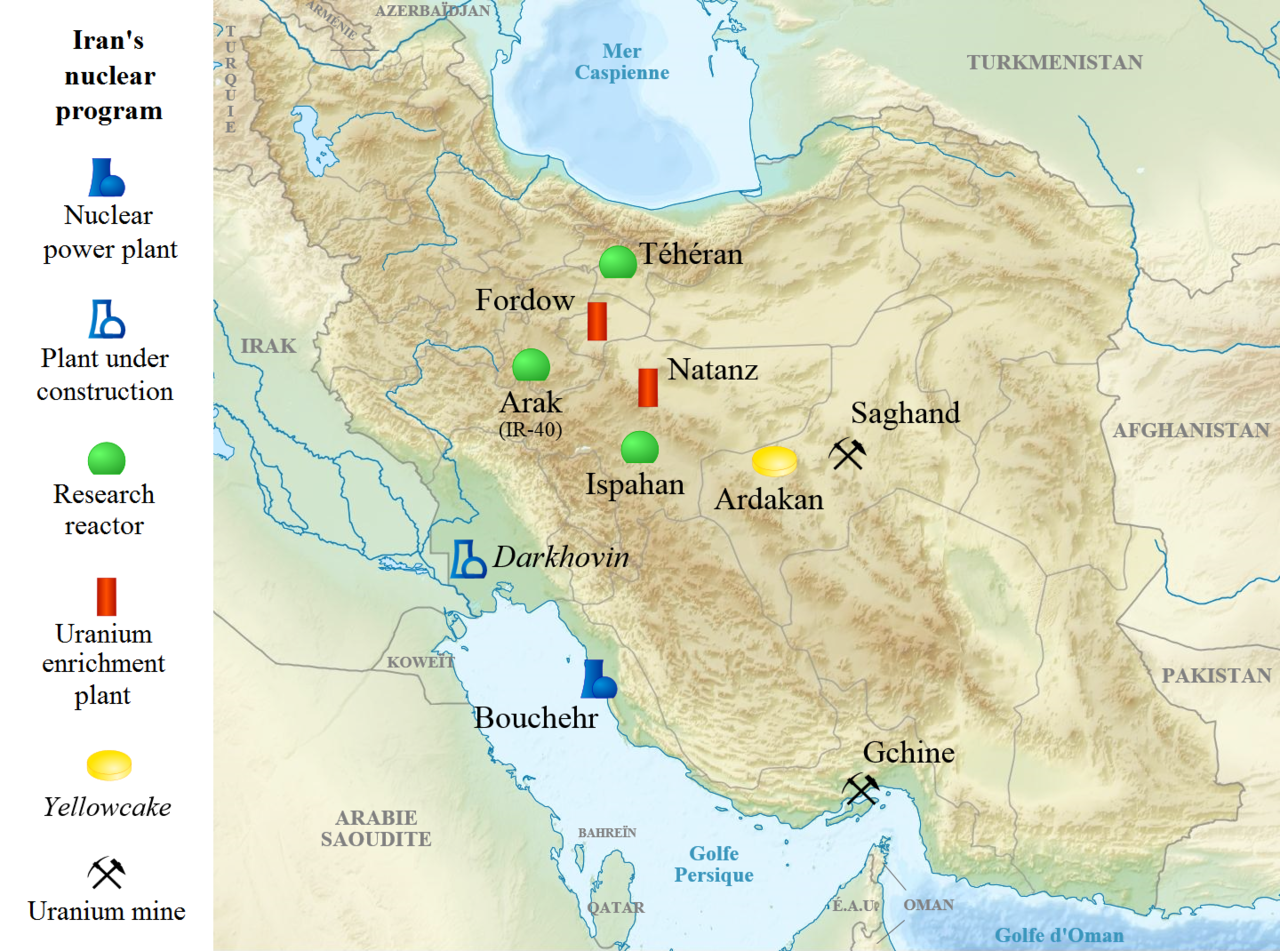
The iran missile attack risk index is designed to answer a practical question that raw range maps cannot: which nodes face the highest operational stress in the first wave, and how quickly can that stress degrade mission continuity? Range is necessary but incomplete. The index weights warning-time compression, interception geometry, infrastructure concentration, and recovery speed because modern escalation is decided as much by continuity as by impact count. In other words, this model asks not only where a missile can land, but where repeated pressure can cause the largest strategic slowdown.
Public discussion around iran missile attack often assumes the nearest target is the riskiest target. That assumption fails in systems with uneven redundancy. A farther base with dense command functions and weak backup routing can be more fragile than a closer base with hardened recovery doctrine. Similarly, a high-profile target can absorb a strike tactically but still preserve output if repair and command pathways remain intact. The index therefore treats risk as a composite score, not a single-distance measure.
How the Iran Missile Attack Risk Index Works
The model uses five weighted components. First, time-to-threat estimates warning compression for likely target classes. Second, defense saturation pressure estimates how quickly interception systems can be stressed under repeated volleys. Third, infrastructure concentration captures how much mission output depends on a small physical footprint. Fourth, recovery resilience estimates runway, command, and logistics restoration capacity. Fifth, cross-domain coupling captures how cyber, maritime, or proxy pressure can amplify missile effects.
Each component is scored from 0 to 100, then normalized into a composite risk band. Scores are intentionally directional and conservative. The purpose is to rank relative exposure, not publish deterministic forecasts. During quiet periods, the model updates slowly. After confirmed us attacks iran or high-confidence retaliation signals, weight sensitivity increases because timing and volume assumptions can change quickly.
Component Weight Table
| Component | Weight | What It Measures | Why It Matters |
|---|---|---|---|
| Time-to-threat | 25% | Warning window compression | Short windows reduce defensive decision quality |
| Defense saturation pressure | 20% | Interception stress under volume | Saturation can outpace technical interceptor capability |
| Infrastructure concentration | 20% | Mission dependence on dense nodes | Dense nodes create high disruption leverage |
| Recovery resilience | 20% | Repair and continuity capacity | Fast recovery limits strategic effect of strikes |
| Cross-domain coupling | 15% | Missile effects amplified by other domains | Combined pressure drives non-linear disruption |
Why Distance Alone Misclassifies First-Wave Risk
Distance is visually intuitive, which is why it dominates public maps. But operational outcomes are usually shaped by system behavior after first impact. A base that can disperse assets, reroute commands, and restore runway function quickly may experience high tactical stress but low strategic degradation. A base with weaker redundancy may experience the opposite. The risk index therefore asks: how much capability remains executable 24, 48, and 72 hours after first-wave pressure?
This distinction becomes critical when interpreting search demand around iran response to us strikes. Audiences often interpret capability headlines as immediate certainty. Analysts instead examine whether launch support, proxy activity, and command messaging converge into executable timing. Capability without timing convergence keeps risk elevated but uncertain. Capability with timing convergence shifts risk sharply upward.
Sample Scoring Across Exposure Bands
The table below shows how relative scoring works. Values are illustrative and represent a standardized modeling pass, not classified intelligence. The key point is ranking logic: a site with moderate distance can still rank high if it combines compressed warning time, dense critical infrastructure, and limited repair depth. A site with short distance can rank lower if defensive and recovery layers are robust.
| Node Class | Time-to-Threat | Infra Concentration | Recovery Resilience | Composite Band |
|---|---|---|---|---|
| Regional command-air node | High | High | Medium | Very High |
| Dispersed support base | Medium | Low-Medium | High | Medium |
| Maritime logistics chokepoint | Variable | High | Medium-Low | High |
| Hardened isolated installation | Medium | Low | High | Low-Medium |
Interception Density and Saturation: The Hidden Variable
Interception capability is often reported as a platform count, but platform count does not equal sustained protection. The relevant metric is interception density over time: how many intercept opportunities can be generated under repeated salvos, while maintaining tracking quality and command discipline. Saturation risk grows when warning windows shrink and when launches are staggered to force constant re-tasking. This is why defense quality is temporal, not static.
For model users, saturation scenarios should be tested with uncertainty bands. A system might perform at high efficiency in the first exchange and materially lower in later exchanges due to fatigue, reloading constraints, or command traffic congestion. These second-order effects can shift a medium-risk node into high-risk status even with unchanged distance metrics.
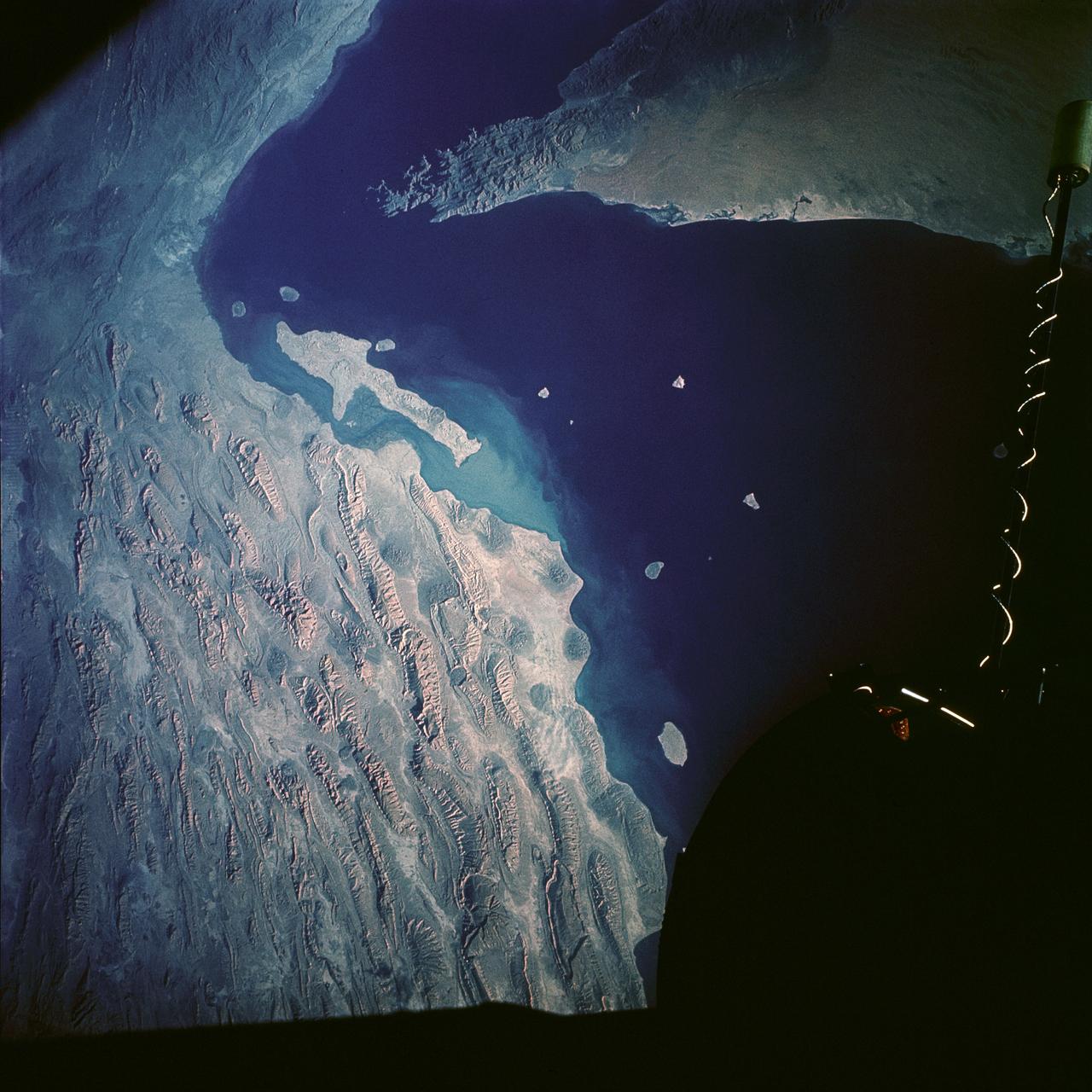
How Market and Maritime Signals Feed the Index
The index also incorporates non-military signals because escalation impacts propagate through logistics and insurance networks. If shipping advisories, war-risk premiums, and rerouting behavior spike near the same time as military posture changes, the probability of sustained pressure generally increases. For this reason, our scoring model references inputs aligned with the Strait of Hormuz shipping freeze analysis. Missile and maritime systems are coupled in real crises; treating them separately underestimates combined risk.
Likewise, legal and political framing can alter expected duration even without immediate tactical changes. Readers should cross-reference this page with are we at war with Iran now and is Iran going to attack the U.S. because intent and authority signals frequently move faster than observed launch behavior.
72-Hour Update Protocol for Risk Teams
In active windows, we recommend a 72-hour update loop. In hours 0-24, prioritize new launch-support evidence and official language shifts. In hours 24-48, check persistence and cross-domain coupling signals. In hours 48-72, evaluate whether target classes or launch timing patterns broaden. If broadening appears, increase composite risk bands with explicit uncertainty notes. If broadening does not appear, maintain elevated watch status with bounded escalation assumptions.
The model should never be published without confidence qualifiers. Confidence prevents false precision, and false precision is one of the largest public-risk problems during conflict spikes. Decision-makers need ranges, not performative certainty.
Scenario Stress Testing: What Breaks the Model First?
Every risk index has failure points, and transparent modeling requires naming them. In this framework, the first stress point is launch-volume uncertainty. If volume estimates are too low, saturation risk is understated and composite scores lag reality. The second stress point is deception and decoy behavior that distorts early signal interpretation. The third is recovery overestimation: if repair and continuity assumptions are too optimistic, resilience scores inflate and exposure bands look safer than they are. These failure points are why the index uses uncertainty multipliers during active escalation windows.
Stress testing also includes behavioral shocks. A change in command doctrine, an unexpected proxy surge, or abrupt maritime disruption can alter risk pathways faster than baseline assumptions can absorb. To compensate, model governance includes trigger rules that force immediate recalculation when specific high-impact conditions appear. This approach does not eliminate error, but it reduces lag and keeps public-facing outputs aligned with evolving realities.
A practical example is coupling effects from shipping disruption. If freight and insurance signals deteriorate rapidly, support and resupply pathways for regional operations may tighten, which in turn can shift defense and recovery assumptions. That cross-domain linkage is why the index references both military and market indicators rather than treating them as separate worlds.
Node-Level Profiles: Why Similar Distances Produce Different Scores
To make the model usable, node-level profiles classify sites by functional dependency rather than geography alone. A command-dense air hub, a logistics transfer node, and a hardened isolated installation can sit within similar distance rings yet produce very different risk outcomes. The decisive factors are dependency concentration and substitution pathways. If a node has few substitutes, disruption risk rises even if kinetic probability is moderate. If substitutes are abundant and preplanned, risk can remain manageable despite closer range exposure.
Node profiling also improves communication. Decision-makers often ask for one-number answers, but one-number answers can hide operational tradeoffs. Profile-based reporting preserves nuance by showing where risk comes from and what mitigation levers exist. In conflict periods, this can guide resource allocation more effectively than broad regional averages.
| Node Profile | Dependency Concentration | Substitution Depth | Model Sensitivity | Mitigation Priority |
|---|---|---|---|---|
| Command-dense hub | Very High | Low-Medium | High to timing shocks | Continuity and dispersion |
| Fuel and sustainment node | High | Medium | High to queue disruptions | Stock and routing redundancy |
| Dispersed support base | Medium | High | Medium | Interoperability maintenance |
| Hardened isolated site | Low | Medium-High | Low to moderate | Sustain long-duration readiness |
Governance: Keeping the Iran Missile Attack Risk Index Credible
Credibility depends on repeatable governance. Each update should document input changes, confidence shifts, and rationale for score movement. Without this audit trail, the index becomes narrative-driven instead of evidence-driven. Governance rules also prevent "headline chasing," where scores move because public anxiety rises rather than because inputs changed materially. During escalation, this discipline is essential for maintaining analytical integrity.
Governance also requires clear role separation between data ingestion, scoring, and publication review. Separation reduces confirmation bias and makes it easier to challenge assumptions before release. For public communication, each release should include concise caveats and links to related explainers such as war-threshold legal analysis and retaliation scenario modeling. These links help readers understand what the index can answer and what it cannot.
The index is most useful when treated as a living diagnostic, not a prediction machine. It ranks evolving exposure so teams can prioritize monitoring and mitigation. It does not claim certainty about exact launch timing or exact impact outcomes. That distinction is essential for responsible analysis in high-volatility cycles.
For operational users, the final quality check is backward validation. After each major event window, compare model outputs with observed disruption metrics such as sortie delays, recovery duration, and logistics throughput changes. If the model overpredicted repeatedly in one node class, adjust sensitivity weights downward. If it underpredicted in another class, increase sensitivity and document why. This loop keeps the index tied to outcomes rather than assumptions and improves trust for repeated use.
Backward validation also helps communication clarity. Readers are more likely to trust updated scores when they can see how the model learned from prior windows. Transparent adjustment policy turns a static article into an accountable analytical product, which is the standard required for sustained coverage of a moving crisis environment.
In operational practice, teams should archive each model version with input snapshots and confidence notes. Versioning prevents hindsight bias and allows rapid audits when escalation moves faster than expected. It also helps cross-functional teams align decisions because everyone can reference the same scored baseline before debating next-step mitigation priorities.
Finally, publish score deltas with plain-language interpretation. A five-point shift should explain whether change came from timing risk, saturation assumptions, or resilience degradation. Delta transparency turns technical scoring into actionable decision support for both expert and non-expert readers.
Model clarity improves when every major score change is paired with a "what would reverse this move" note. Reversal criteria keep analysis grounded and prevent one-direction narrative drift during uncertain escalation phases.
Combined with version history, reversal notes help teams separate temporary shock from durable structural change.
FAQ: Iran Missile Attack Risk Index
How is the Iran missile attack risk index calculated?
The index blends warning-time, saturation, infrastructure concentration, recovery resilience, and cross-domain coupling into a weighted composite score.
Why can a farther node rank riskier than a closer node?
Fragility, dependency concentration, and slower recovery can outweigh distance and create higher strategic disruption risk.
What is the largest uncertainty right now?
Timing and volley coordination remain the biggest unknowns. Capability exists, but execution window confidence changes quickly.
How often should this index update in escalation periods?
At least every 12 to 24 hours, with immediate revisions when posture or target scope materially changes.
External references: CSIS Missile Threat, U.S. Missile Defense Agency, SIPRI, IAEA.